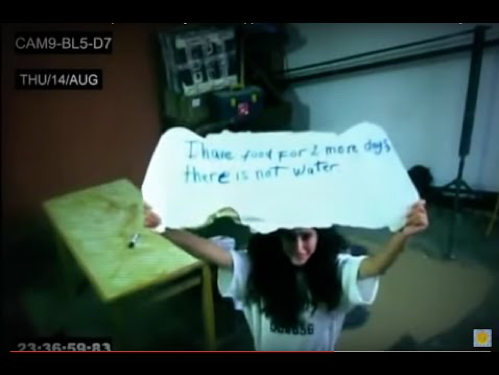
Human trafficking is rampant in our country, but not often mentioned. It happens in the shadows, on the dark web, is hard to track, and tough to talk about.
The crime of human trafficking—defined by the U.S. Department of Homeland Security as modern-day slavery that “involves the use of force, fraud, or coercion to obtain some type of labor or commercial sex act—is notoriously difficult to prosecute. Victims, who are mostly women and children, often lack legal documentation and many fear reprisals if they go to authorities. Therefore perpetrators go to great lengths to conceal their behavior by laundering money and keeping their operations quiet.
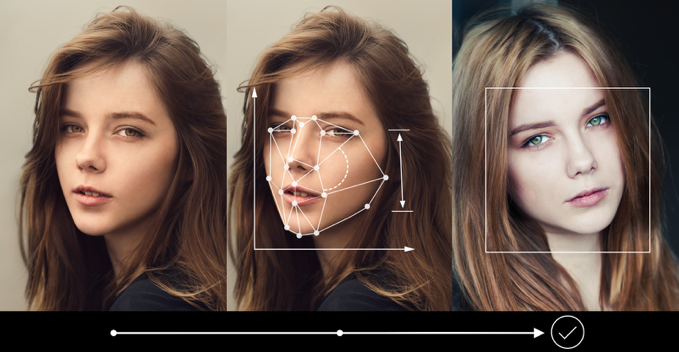
Recently, law enforcement agencies and organizations that help victims of human trafficking have begun using artificial intelligence tools to overcome this lack of visibility. By sorting through data and recognizing patterns faster than any human could, AI tools are helping activists and investigators crack down on buyers of sex, identify trafficking victims and follow illicit money trails.
“Imagine the techniques that Google and Facebook are using to make a
profit—understanding people, the way they connect, what their interests are,
what they might buy or the activities they engage in,” says Dan Lopresti,
professor and chair of the department of science and engineering at Lehigh
University’s P.C. Rossin College of Engineering and Applied Science. “We
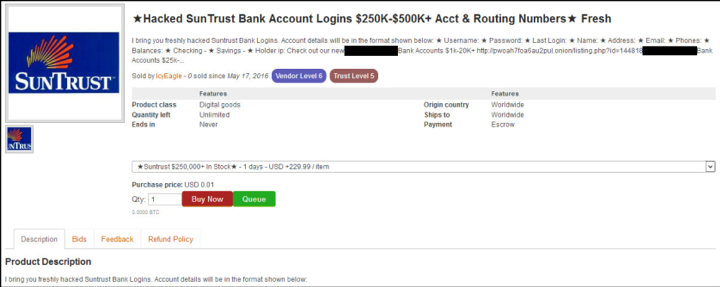
can apply those same techniques—data mining, text mining, what’s called graph
mining—AI that’s being used for legitimate and really profitable purposes, to
track these illicit behaviors.”
Lopresti is involved with the Regional Intelligence and Investigation Center (RIIC) in Allentown, PA. Launched in 2013, the RIIC has “revolutionized” the way area police departments “analyze and share collected data to solve crimes,” according to the office of Lehigh County District Attorney James Martin.
Lopresti, who is an expert in document analysis and pattern recognition, is working with RIIC Director Julia Kocis, prosecutors, law enforcement officials and other Rossin College computer science and engineering faculty members to help overcome the challenges of turning vast amounts of data, primarily from police incident reports, into something useable, despite limited resources.
“If an expert sits down and reads enough of these, he or she will find a common thread—this person is related to this place, which is related to this activity, which is related to this other person,” he says. “The trouble is, they’ve got millions of these reports and just don’t have enough time to read through them. We’re developing natural language techniques, text mining and data mining techniques that are oriented to processing lots of data to identify patterns of behavior that would reflect illegal activities related to human trafficking.”
Because human trafficking is a $150 billion-per-year criminal industry, many companies are joining the fight and helping out. IBM worked with the STOP THE TRAFFIK (STT) coalition to develop a new cloud-hosted data hub that allows financial institutions to run AI and machine learning tools against their data sets to detect “specific human trafficking terms and incidents.” AI also allows the data hub to take in open-source data — including thousands of news feeds each day — to help analysts more easily identify the characteristics of human trafficking incidents.

Entrepreneur Josh McAfee, a former law enforcement officer and loss-prevention executive, is the founder and CEO of McAfee Institute, a Peoria, Illinois-based business that trains corporations and law enforcement agencies to battle cybercrime and fraud. But what brings him the most satisfaction is locating victims of human trafficking.
Since 2011, his company has helped bring back about 1,900 human-trafficking victims, 1,000 of them children.
He now teaches a course on human trafficking to an average of 150 to 200 people a month. “We’re developing leaders in the classroom, so they can go out and utilize our techniques within their organizations. It multiplies our success and enables us to make a huge impact,” says McAfee. “Growing up, I always had a passion for law enforcement. I wanted to get out there and fight crime, get the bad guys–you know, help people. That’s why I became a law enforcement officer right out of college. To be able to do this kind of work in my business is everything to me. It’s what I was born to do.”