Playing
outside with your grandchildren, casting a fishing line or running a marathon
can seem like harmless, healthy fun. But physical activity could lead to denial
of Social Security disability benefits if your activity shows up on Facebook or
Instagram. Is it fair for the government to go through your social media? On
the other hand, is it fair for you to apply for benefits if you can do these
activities?
These
are all questions the Social Security Administration is weighing, as Acting
Social Security Commissioner Nancy A. Berryhill has told Congress in written explanations over the last
week. Facebook and other social media feeds are already being reviewed if
agency investigators suspect someone is fraudulently collecting benefits and
they are looking for corroboration, the agency said in the documents it gave to
lawmakers. But now the agency is “evaluating how social media could be used by
disability adjudicators in assessing the consistency and supportability of
evidence in a claimant’s case file,” Berryhill said in the submission to
Congress.
The
idea has drawn praise as well as criticism — praise because more attention to
people’s social media could cut down on fraud, some say. Fraud and abuse do exist in the program, and it should
be weeded out to protect taxpayers and legitimate claimants.
The Pros
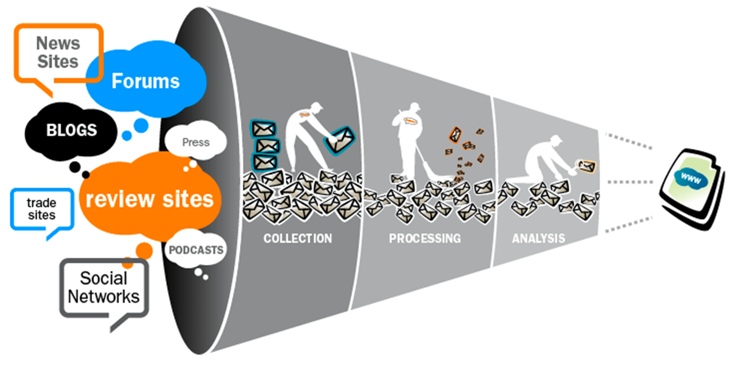
Mark Hinkle, acting press officer for the SSA,
notes that the agency uses data analytics and predictive modeling to detect
fraud, and has created new groups dedicated to detection and prevention. Asked
to comment on plans for expanded use of social media to detect fraud, he
confirmed that SSA investigative units already use social media, and that the
agency has “studied strategies of other agencies and private entities to
determine how social media might be used to evaluate disability applications.”
The
Social Security Administration said that in December, 8.5 million people of all
ages received a total of $10.5 billion in disability benefits, with an average
monthly sum of $1,234. It said 68 percent of the private-sector workforce has
no long-term disability
insurance.
The
risk of disability rises with age, and people are twice as likely to collect
disability benefits at age 50 as at age 40 — and twice as likely at age 60
compared to age 50, according to the Center on Budget and Policy Priorities, a
liberal Washington think tank.
“Social
media can provide valuable evidence to support or deny individuals’ disability
claims,” Rachel Greszler, a research fellow at the Heritage Foundation, a
conservative Washington think tank, wrote last year. “For
example, a disability claimant may say that she is unable to leave her home,
while her social media pictures show her out and about regularly.”
In one case, a 57-year-old Louisiana man pleaded guilty last
month to theft of government funds. He had received $2,177 a month in benefits
— a total of $242,000 — while employed by companies that did demolition work
and job site cleaning. He also operated heavy construction equipment. He told
federal investigators that the companies had been registered in the names of
family members, rather than his own name, “so y’all wouldn’t find out about
it,” according to court records.
In its
latest financial report, Social Security estimated that it made $3.4 billion in
overpayments to disability insurance beneficiaries in 2017, in part because of
their failure to report work activities. The program has been “riddled with
problems, including fraud and abuse,” said Greszler. When people who can work
collect benefits, she said, “it drains the system for those who truly cannot
work and support themselves.”
The Cons
Advocates
for people with disabilities say the use of social media in this way would be
dangerous because photos posted there do not always provide reliable evidence
of a person’s current condition. Someone may not want to upload a picture or
video that shares how he or she deals with a disability on a daily basis.
Social
media reviews could also delay the time it takes for applicants who are already
out of work to be approved. “This proposal starts with the discriminatory
assumption that people with disabilities do nothing socially in the community,
or have lives, so that anything the person does on social media can be
classified as some form of fraud,” said Eric Buehlmann, deputy executive
director of public policy at the National Disability Rights Network, a
nonprofit membership advocacy group. He told AARP that methods to detect fraud
already exist. If the Social Security Administration “is interested in rooting
out fraud,” Beuhlmann said, “spying on people’s social media accounts
is not the way to do it.”
“It may be
difficult to tell when a photograph was taken,” said Lisa D. Ekman, a lawyer
who is the chairwoman of the Consortium for Citizens with Disabilities, a
coalition of advocacy groups. “Just because someone posted a photograph of them
golfing or going fishing in February of 2019 does not mean that the activity
occurred in 2019.”
Program statistics do not support the allegation that SSDI is
riddled with fraud and abuse. In the government’s fiscal-year 2018, the SSA’s
Office of the Inspector General (OIG) reported about $98 million in recoveries,
fines, settlements/judgments, and restitution as a result of Social Security
fraud investigations. The OIG states that most the recovered funds were from
recipients of SSDI and Supplemental Security Income (SSI), a means-tested
welfare program for low-income seniors, blind and disabled people.
That sounds like big money. But in fiscal 2018, the SSA paid out
$197 billion to beneficiaries of SSDI and SSI. And keep in mind that the
recovered $98 million was for benefits paid out over several years, not just in
2018. SSA data shows that the rate of overpayments for all its programs was
well under 1% of benefit payouts in each of the last three fiscal years – and
not all improper payments are fraud.
More often, overpayments occur due to administrative delays at
the SSA in making adjustments to benefit amounts due to errors and paperwork
snafus. A federal government list of programs at highest risk for making
improper payments compiled by the Office of Management and Budget does not even
mention Social Security.
Greszler has readily acknowledged that fraud rates are low.
“Outright fraud is actually a pretty small component of the program’s
problems,” she said. “Most people perceive fraud as a big issue but what they
might consider fraud – people receiving benefits when they have the ability to
work – is often just abuse of the system by taking advantage of certain rules
and structures that allow people who can perform some work to nevertheless
receive benefits.”
What constitutes abuse of the rules? An example, she said, would
be claiming SSDI and receiving unemployment benefits at the same time, or
claiming based on the argument that a disability prevents a worker from performing
certain types of jobs, Greszler and other SSDI critics often point to the rise
of SSDI applications and award grants coincident with the rise of unemployment
during the Great Recession as evidence of abuse.